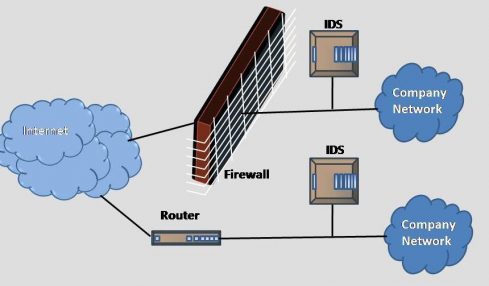
What Are Intrusion Detection Systems?
With computer hackers and identity thieves getting more computer literate, the security your computer needs to keep them out has to always stay at...
With computer hackers and identity thieves getting more computer literate, the security your computer needs to keep them out has to always stay at...

It is worth bearing in mind that, when you are deciding which web conferencing application to utilize, none of the applications currently available will...
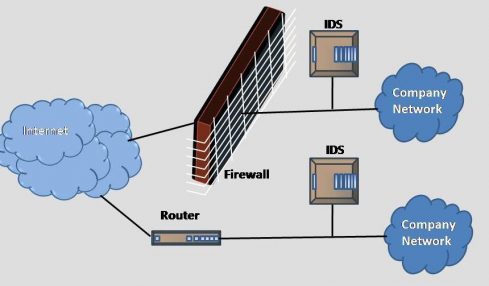
The CPU of a computer is the part of it which performs all of its logical and arithmetic calculations. All calculations are done by...

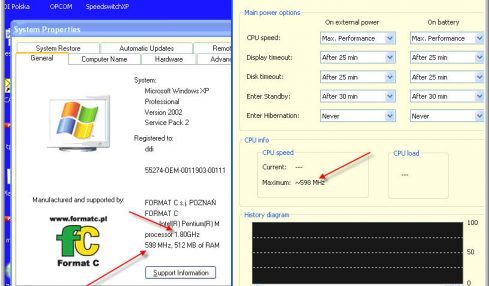
So we’ve finally left the era of the Internet crawling along, taking forever to load anything – we’ve entered the high speed age, where...

Isn’t it interesting how we always seem to take for granted some of the most significant technological breakthroughs that have helped propel our society...
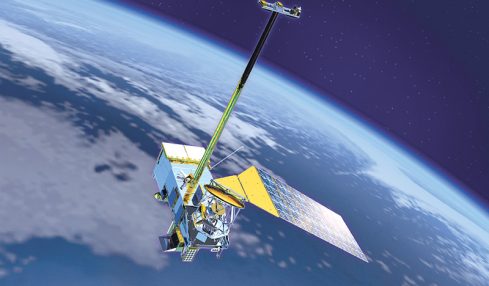
As technology advanced forward, many of the things we’ve taken for granted for years are being reborn under the banner of wireless or wireless...

Before you decide to go wireless or not, there are many points to consider. You may be asking yourself if wireless is for you. ...
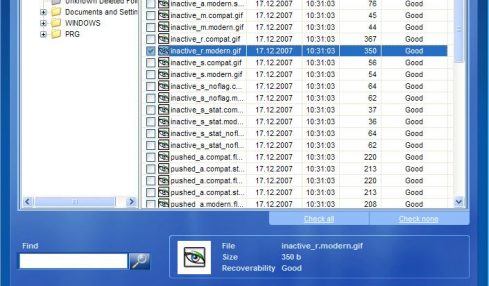
Recovering data lost due to system malfunction or user error requires hours of work preceded by hours of research from unsuspecting victims. Educate yourself...
Recovery Toolbox for Word is a solution for recovery Word, it repairs documents in Microsoft Word format. This MS Word repair tool processes damaged...