
Network Security – The Real Vulnerabilities
Scenario: You work in a corporate environment in which you are, at least partially, responsible for network security. You have implemented a firewall, virus...

Scenario: You work in a corporate environment in which you are, at least partially, responsible for network security. You have implemented a firewall, virus...
Buyer Beware – Ignorance can be a financial waste and a lot of hassals. Before you buy any wireless equipment, you need to be...

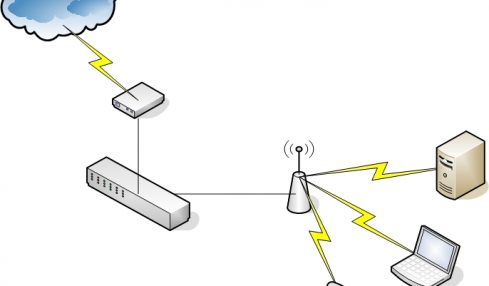
Wireless networks use radio waves instead of wires to transmit data between computers. Here’s how: The Binary Code: 1s and 0s It’s well known...

Media Go makes it easier than ever to take your media with you wherever you go. Transfer music, photos, and videos from your PC...

Used computers are available plenty in number. But, the prime concern is that how it will satisfy the needs of the purchaser. The next...

Inkjet Printers are not only getting better but they also becoming less expensive with time. A branded inkjet cartridge can cost you $30 or...

Engineers have known for years that the pool of these IP addresses would one day run out. Websites and service providers have been experimenting...
What Professionals Use to Recover Microsoft Office Passwords The Microsoft Office Application Suite has dominated the market for many years. The suite offers a...

Satellite Internet has allowed people the freedom of being on the road whilst still having access to the Internet. RV travel allows all the...

Wireless Internet connections aren’t just convenient for you-they also may be convenient for hackers. Fortunately, it isn’t difficult to protect yourself. Wireless systems can...